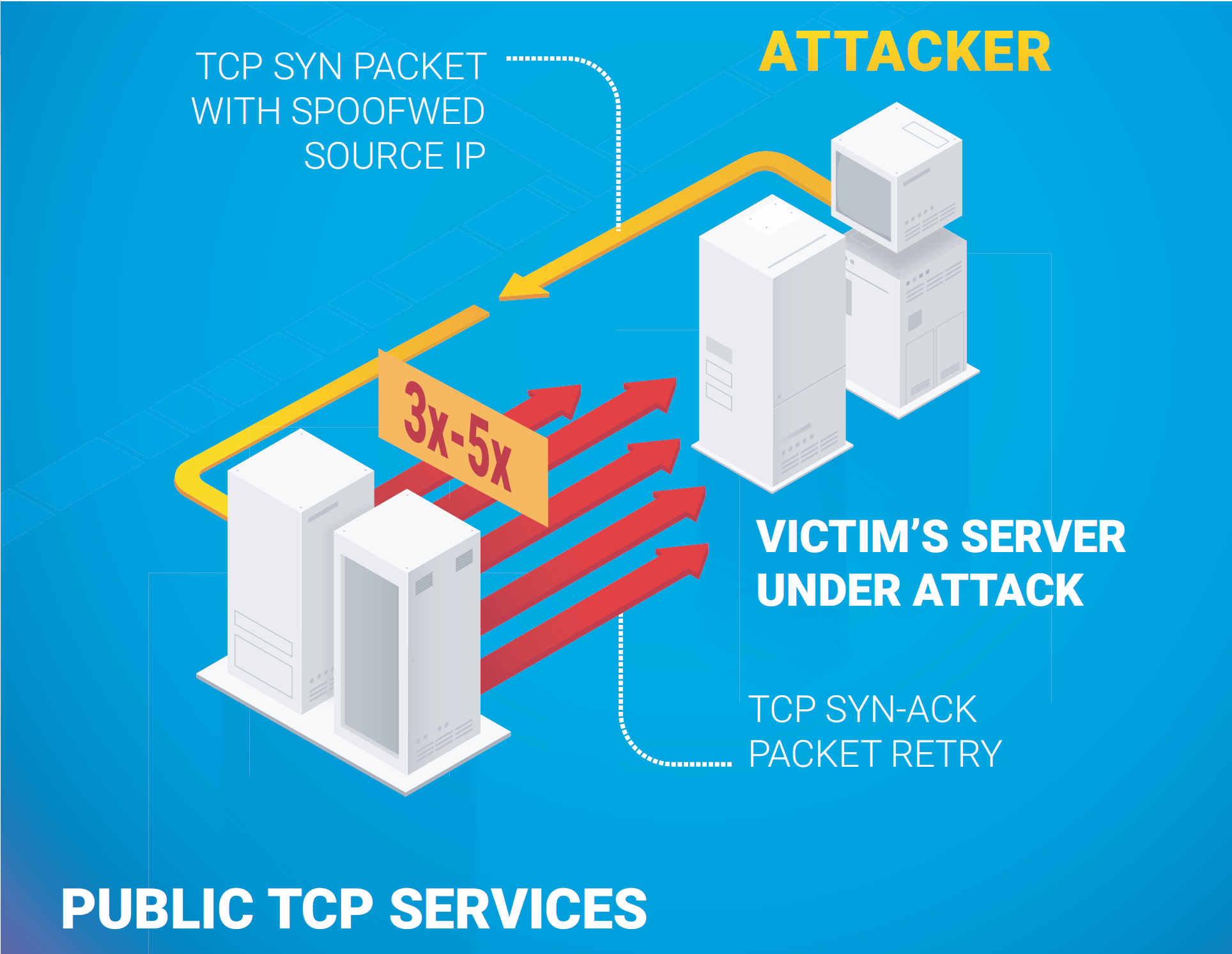
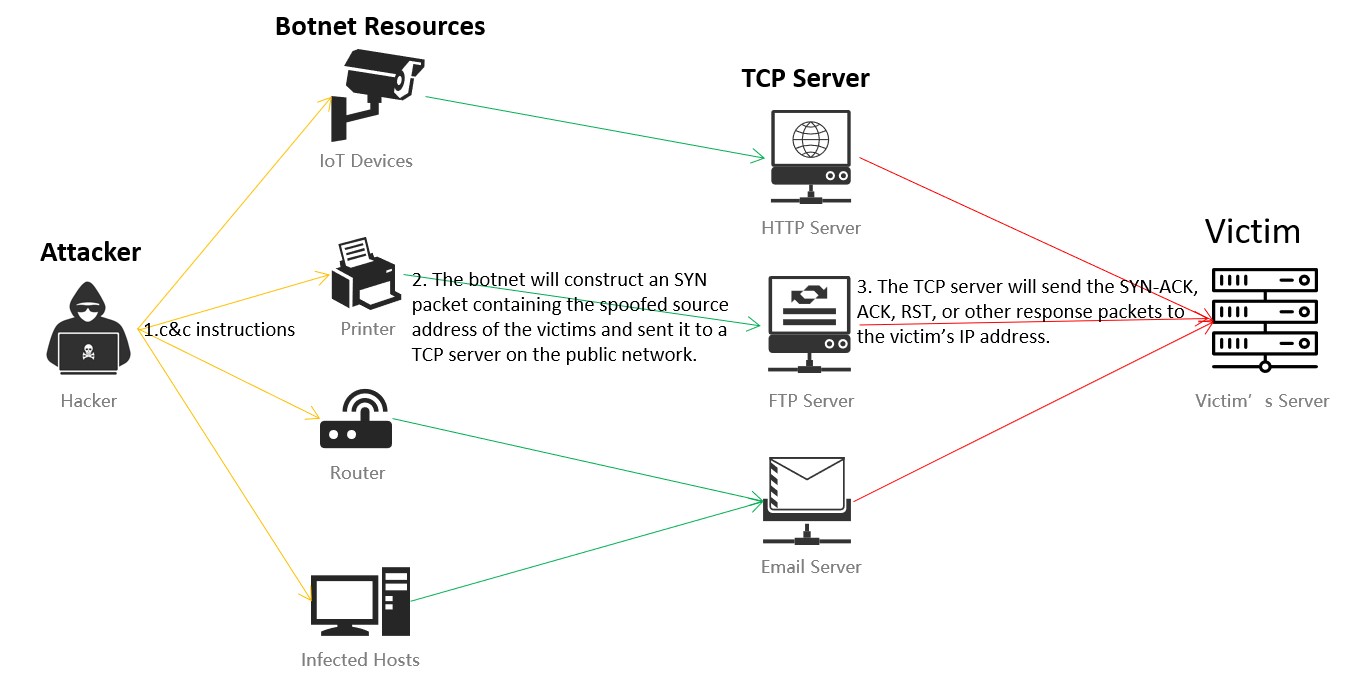
Research and Analysis of Middlebox-based TCP Reflective Amplification Attacks - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.
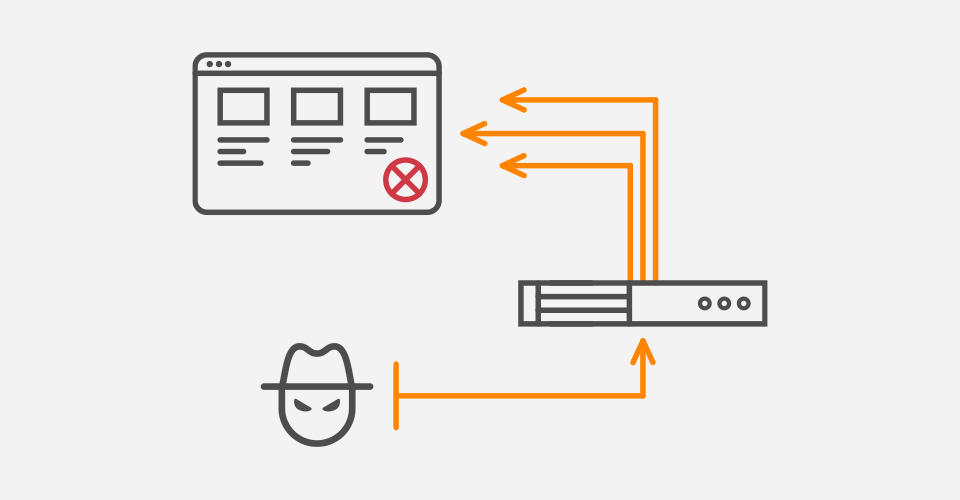
DDoS Attacks That Employ TCP Amplification Cause Network Congestion, Secondary Outages - Security News - Trend Micro HK-EN
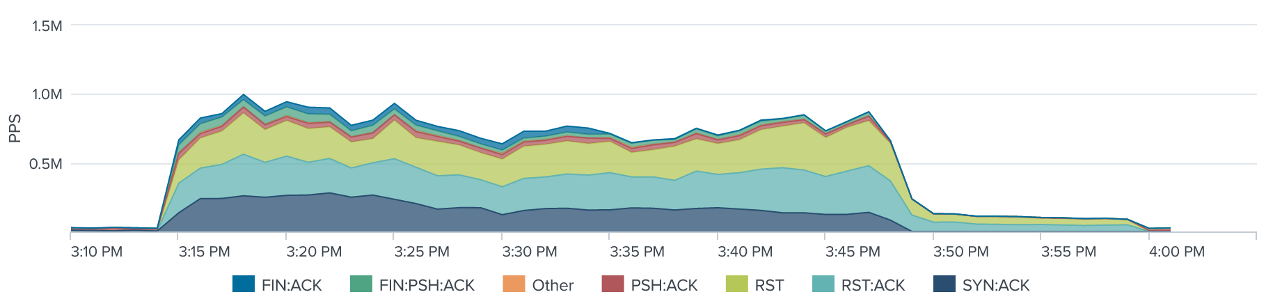
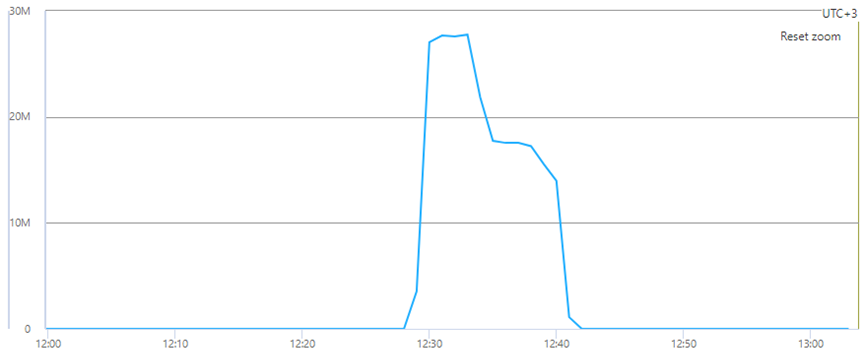
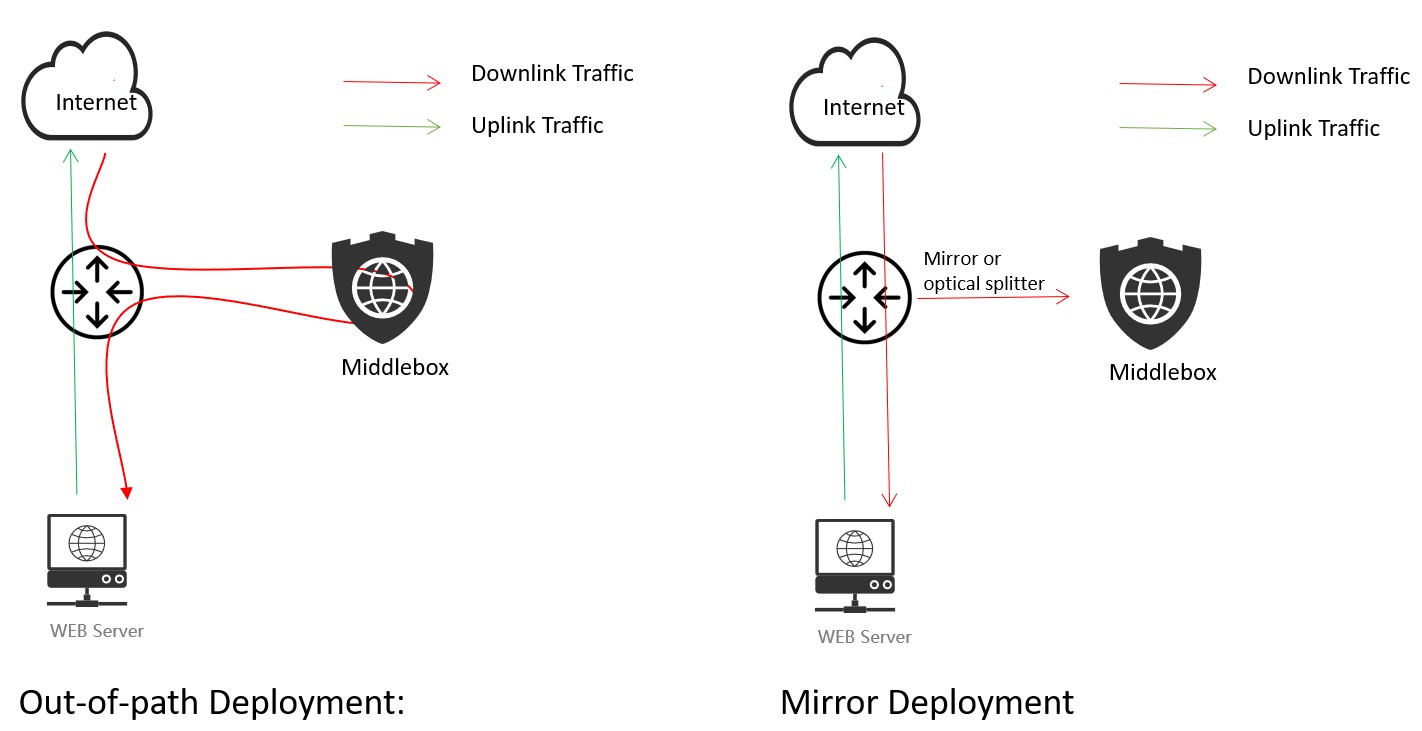
Research and Analysis of Middlebox-based TCP Reflective Amplification Attacks - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.

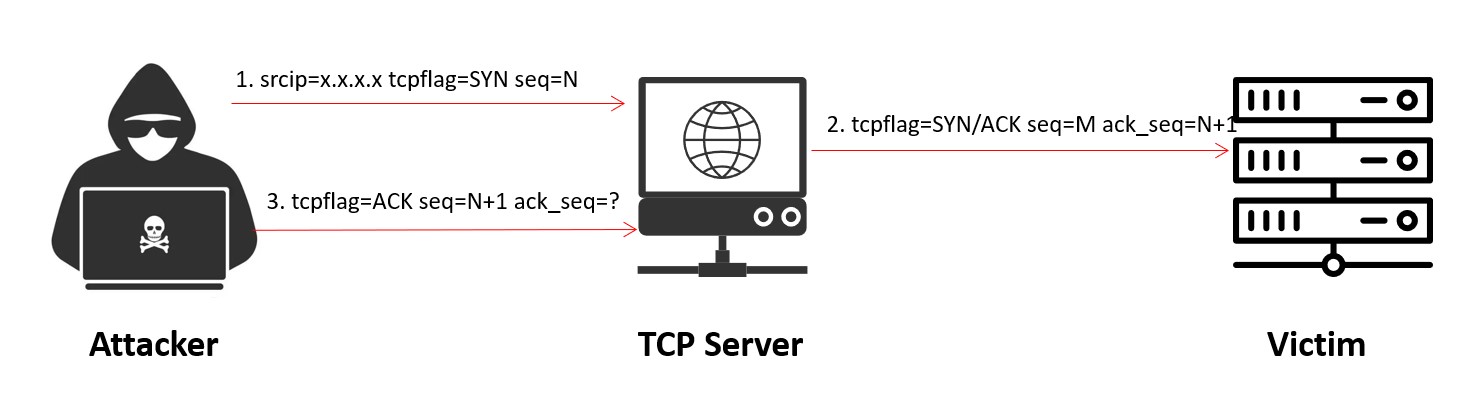
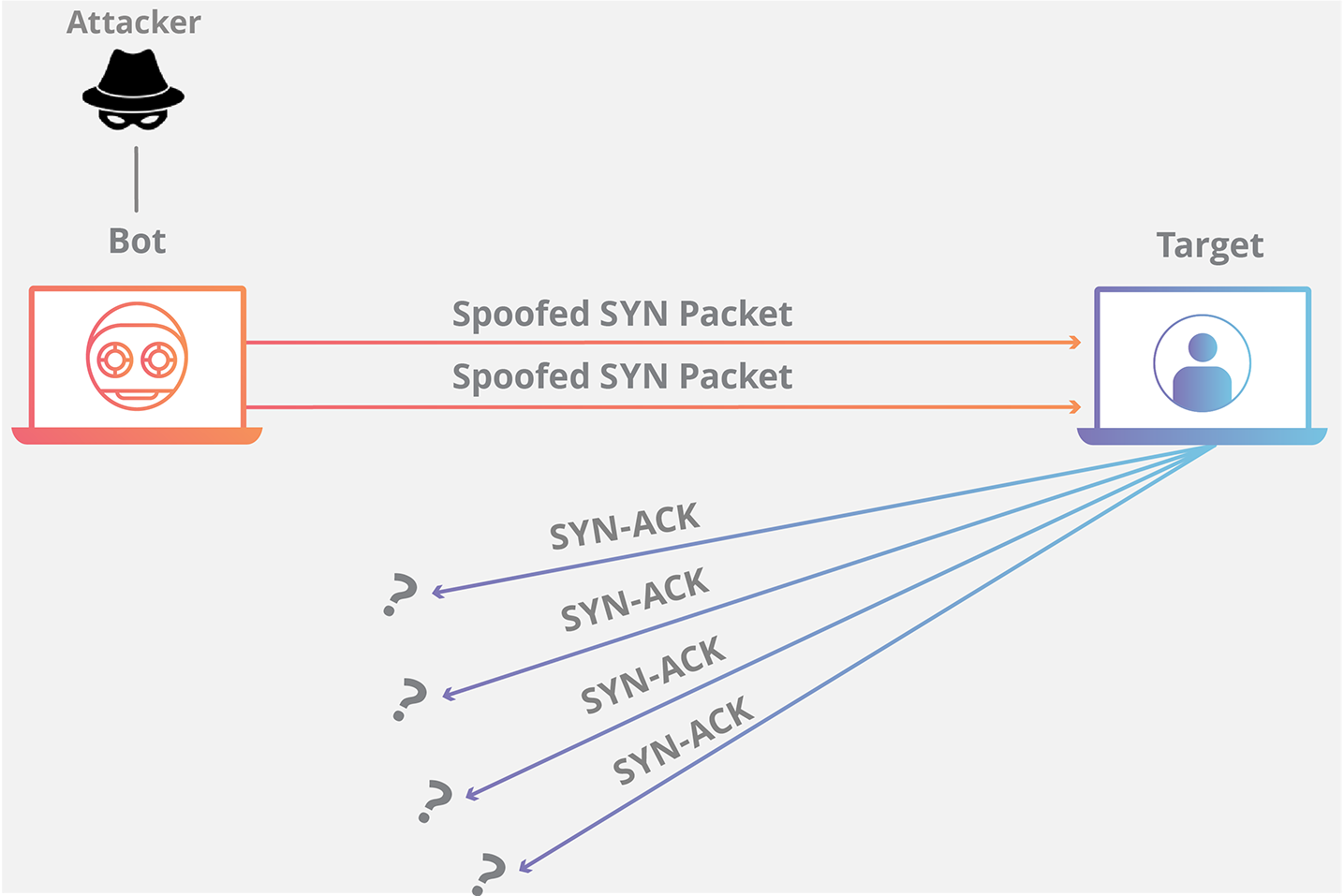
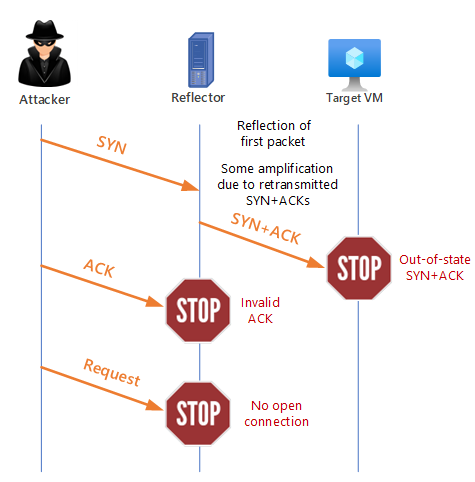
SYN-ACK-ACK proxy flood process. To initiate this attack on Juniper... | Download Scientific Diagram